The Real Deal
Plans for a national ID card face obstacles and opposition
In spite of, or perhaps because of, my 30 years of military service, I remain skeptical of both the efficiency of government and how much government can be trusted to handle large volumes of private information.
It was only last year that an employee of the Department of Veterans Affairs took home the files of 25 million veterans without authorization and against department policy<\m>and it was stolen. In my opinion, the prospect of a national ID card required by the REAL ID Act of 2005 raises serious concerns about privacy, data security, cost, fairness and mission creep that should be fully scrutinized before implementation.
The Bush administration and the 9/11 Commission have promoted the REAL ID system as an important tool for homeland security, but a significant number of computer security experts say its design is flawed and insecure. Privacy advocates have raised strong concerns about an increased risk of privacy loss, identity theft, racial tracking and monitoring of citizens.
While the actual regulations and technical specs are expected to be handed down by the Department of Homeland Security this fall, the expectations are widely understood: States will be required to implement systems and databases to electronically and securely capture, store and share a significant volume of citizen documentation that proves identity, lawful status, date of birth and Social Security number. Each state must be able to share its motor vehicle database with all other states, and the database must include, at a minimum, all the information printed on state driver's licenses, plus drivers' history, including motor vehicle violations and suspensions.
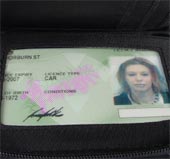
DHS insists the REAL ID Act is an essential tool to fight the war on terror. In its proposed implementation plan, the department found that the threat posed by terrorist travel within the United States demands a systematic and comprehensive ID system. The act aims to weave driver's licenses and state ID cards into a machine-readable ID card with a digital photograph that is necessary to travel on an airplane, open a bank account, collect Social Security payments or take advantage of nearly any government service. States must begin to issue the new federal licenses, mandatory for all "federal purposes," by May 11, 2008, but states can request an extension until Jan. 1, 2010. Extension or not, full compliance is required by 2013. A DHS spokesman has warned that people in states that don't comply by that date will be required to use passports, as no federal agency will accept a state-issued driver's license as a valid form of ID. People will need to use passports at federal buildings and parks and for domestic air travel.
Congress passed the REAL ID Act as part of an emergency military spending and tsunami relief bill, Public Law 109-13, to carry out a proposal suggested by the 9/11 Commission that reported that some of the September 11th hijackers had fraudulently obtained state driver's licenses. But critics argue the plan is misguided, insufficiently privacy protective and prohibitively expensive. The National Governor's Association estimates the cost at $11 billion over five years. States hoping for federal help to comply with REAL ID will have to find other funding sources to pay for the technology, since on July 26, the Senate shot down an amendment that would have earmarked $300 million a year to help states pay for the technology requirements needed to comply. To date, the federal government has provided only $40 million toward implementation. The DHS budget is expected to increase another $50 million on Oct. 1.
In spite of limited federal funding, the scope of REAL ID implementation is very broad. To illustrate the various components of the process, last June, the DHS developed a concept of operations.
First, the REAL ID program governs the external inputs in the state driver's license (DL)/ID issuing system: DL/ID holders and applicants, the identity documents they are required to provide and the card stock that state DMVs will use for card production. While the institutions issuing identity documents are not directly regulated by DHS, they will be impacted by the requirements of the REAL ID program.
Second, the REAL ID program governs the operations of state and territorial DMVs with respect to:
• Processes for verifying the identity of applicants and the identity documents they provide.
• Storage of identity documents.
• Verification of applicant data.
• Appearance and security elements of DL/IDs.
• Security standards for card production and issuance.
• Training and clearances for key DMV employees.
Since the operations of state DMVs are governed by individual state laws and regulations, they may need to be modified based upon the proposed rule.
Third, REAL ID requires verification of applicant data with a number of federally sponsored databases. In addition, federal databases will be accessed as part of the clearance process for DMV employees.
Fourth, communications systems need to be developed or enhanced to query federally-sponsored systems and state DMV databases for data verification. These two data communications processes can be separate and respond to different requirements in the statute and REAL ID implementation. State DMVs will need to query federally sponsored systems, either directly or indirectly, to verify applicant data. On the other hand, state DMVs also will need to query other state DMV databases to ensure that applicants are not previously issued REAL ID-compliant licenses in other states. Finally, all of the components and processes impacted by REAL ID will require assessment of privacy impacts to ensure that data is appropriately safeguarded.
The real issue for states can boil down to the cost of implementing and maintaining the systems required to support REAL ID. Legislatures in 17 states have opposed the act, but most of those objections were related to concerns about paying for REAL ID, and the opposition could dwindle if more federal money is made available.
If the Real ID system is the important tool for homeland security that the administration and 9/11 Commission believe it to be, they should find a way to fund it and put in the safeguards necessary to protect our privacy. If they are not willing to do that, they should stop the charade.